|
|
||
|---|---|---|
| .. | ||
| assets | ||
| README.md | ||
| diagram.png | ||
| main.tf | ||
| outputs.tf | ||
| variables.tf | ||
| versions.tf | ||
README.md
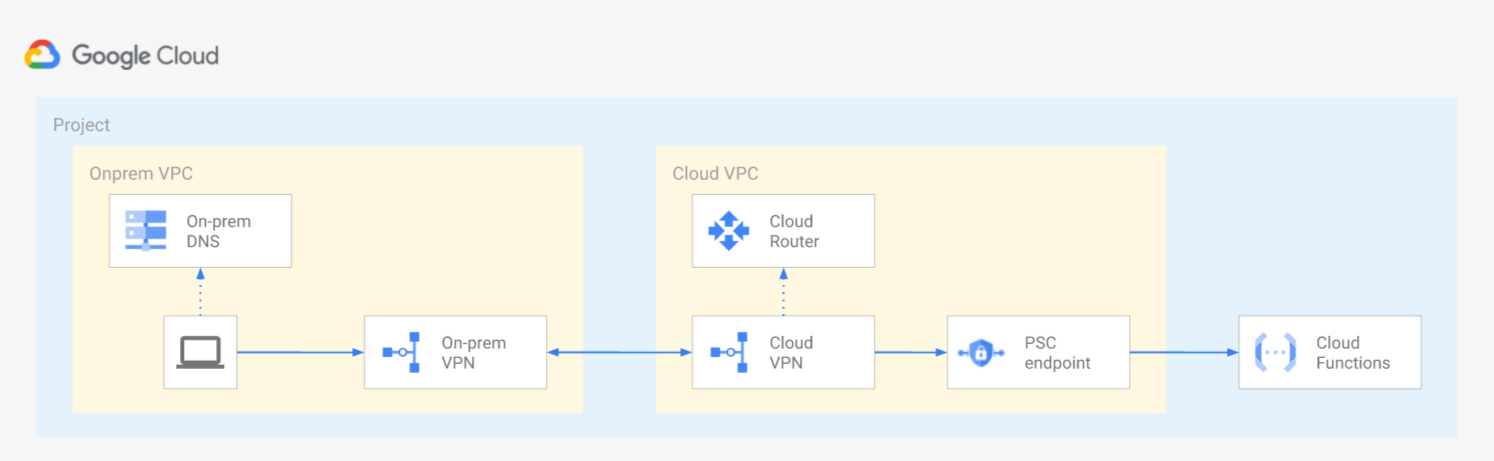
Calling a private Cloud Function from On-premises
This example shows how to invoke a private Google Cloud Function from the on-prem environment via a Private Service Connect endpoint.
According to the documentation, only requests from VPC networks in the same project or VPC Service Controls perimeter are allowed to call a private Cloud Function. That's the reason why a Private Service Connect endpoint is needed in this architecture.
The Terraform script in this folder will create two projects connected via VPN: one to simulate the on-prem environment and another containing the Cloud Function and the Private Service Connect endpoint.
The "on-prem" project contains a small VM that can be used to test the accessibility to the private Cloud Function:
curl https://YOUR_REGION-YOUR_PROJECT_ID.cloudfunctions.net/YOUR_FUNCTION_NAME
Variables
| name | description | type | required | default |
|---|---|---|---|---|
| project_id | Project id. | string |
✓ | |
| ip_ranges | IP ranges used for the VPCs. | object({…}) |
{…} |
|
| name | Name used for new resources. | string |
"cf-via-psc" |
|
| project_create | If non null, creates project instead of using an existing one. | object({…}) |
null |
|
| psc_endpoint | IP used for the Private Service Connect endpoint, it must not overlap with the hub_ip_range. | string |
"172.16.32.1" |
|
| region | Region where the resources will be created. | string |
"europe-west1" |
Outputs
| name | description | sensitive |
|---|---|---|
| function_url | URL of the Cloud Function. |