|
|
||
|---|---|---|
| .. | ||
| __need_fixing | ||
| decentralized-firewall | ||
| filtering-proxy | ||
| filtering-proxy-psc | ||
| glb-and-armor | ||
| glb-hybrid-neg-internal | ||
| ha-vpn-over-interconnect | ||
| hub-and-spoke-peering | ||
| hub-and-spoke-vpn | ||
| ilb-next-hop | ||
| private-cloud-function-from-onprem | ||
| psc-glb-and-armor | ||
| psc-hybrid | ||
| shared-vpc-gke | ||
| README.md | ||
README.md
Networking and infrastructure blueprints
The blueprints in this folder implement typical network topologies like hub and spoke, or end-to-end scenarios that allow testing specific features like on-premises DNS policies and Private Google Access.
They are meant to be used as minimal but complete starting points to create actual infrastructure, and as playgrounds to experiment with specific Google Cloud features.
Blueprints
Calling a private Cloud Function from on-premises
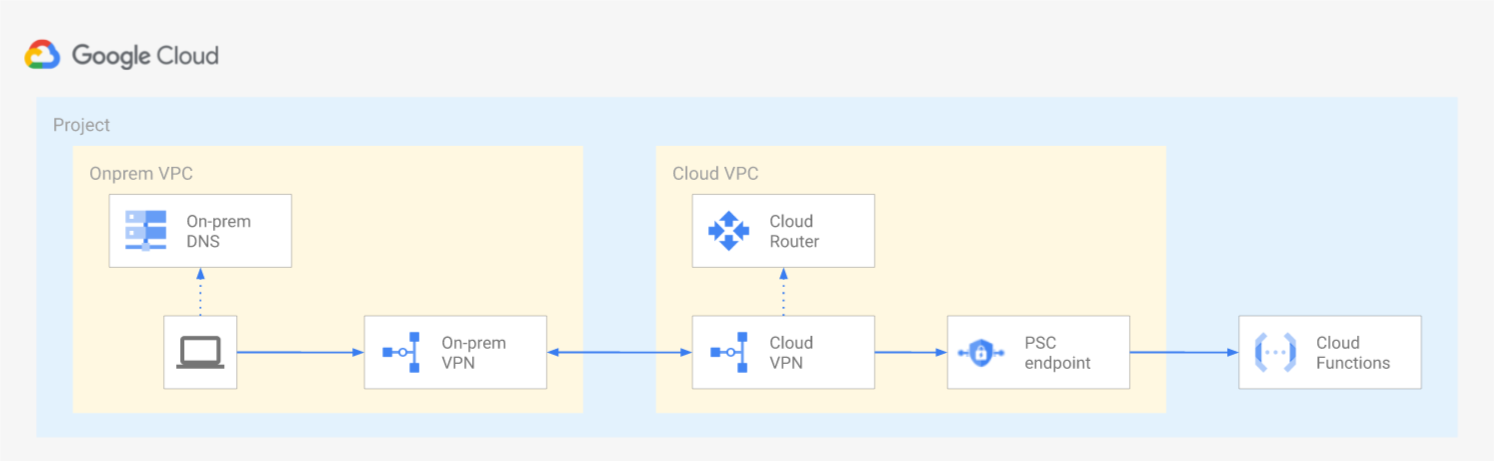 This blueprint shows how to invoke a private Google Cloud Function from the on-prem environment via a Private Service Connect endpoint.
This blueprint shows how to invoke a private Google Cloud Function from the on-prem environment via a Private Service Connect endpoint.
Calling on-premise services through PSC and hybrid NEGs
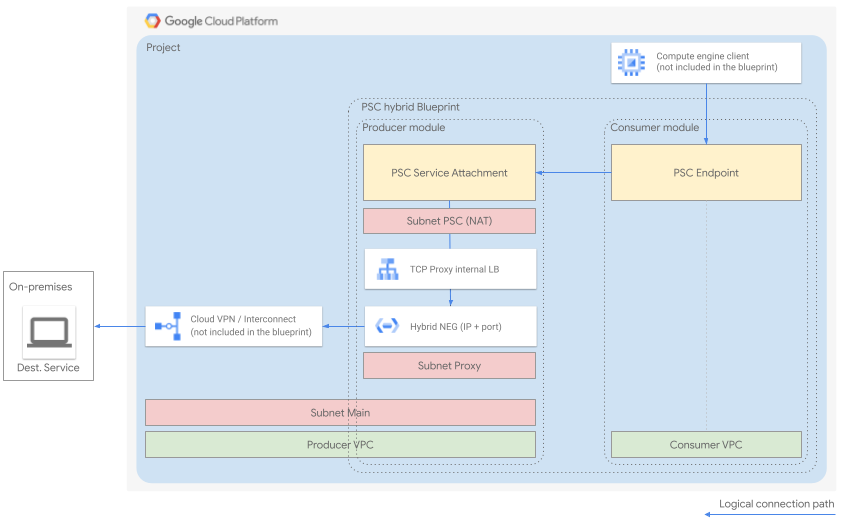 This blueprint shows how to privately connect to on-premise services (IP + port) from GCP, leveraging Private Service Connect (PSC) and Hybrid Network Endpoint Groups.
This blueprint shows how to privately connect to on-premise services (IP + port) from GCP, leveraging Private Service Connect (PSC) and Hybrid Network Endpoint Groups.
Decentralized firewall management
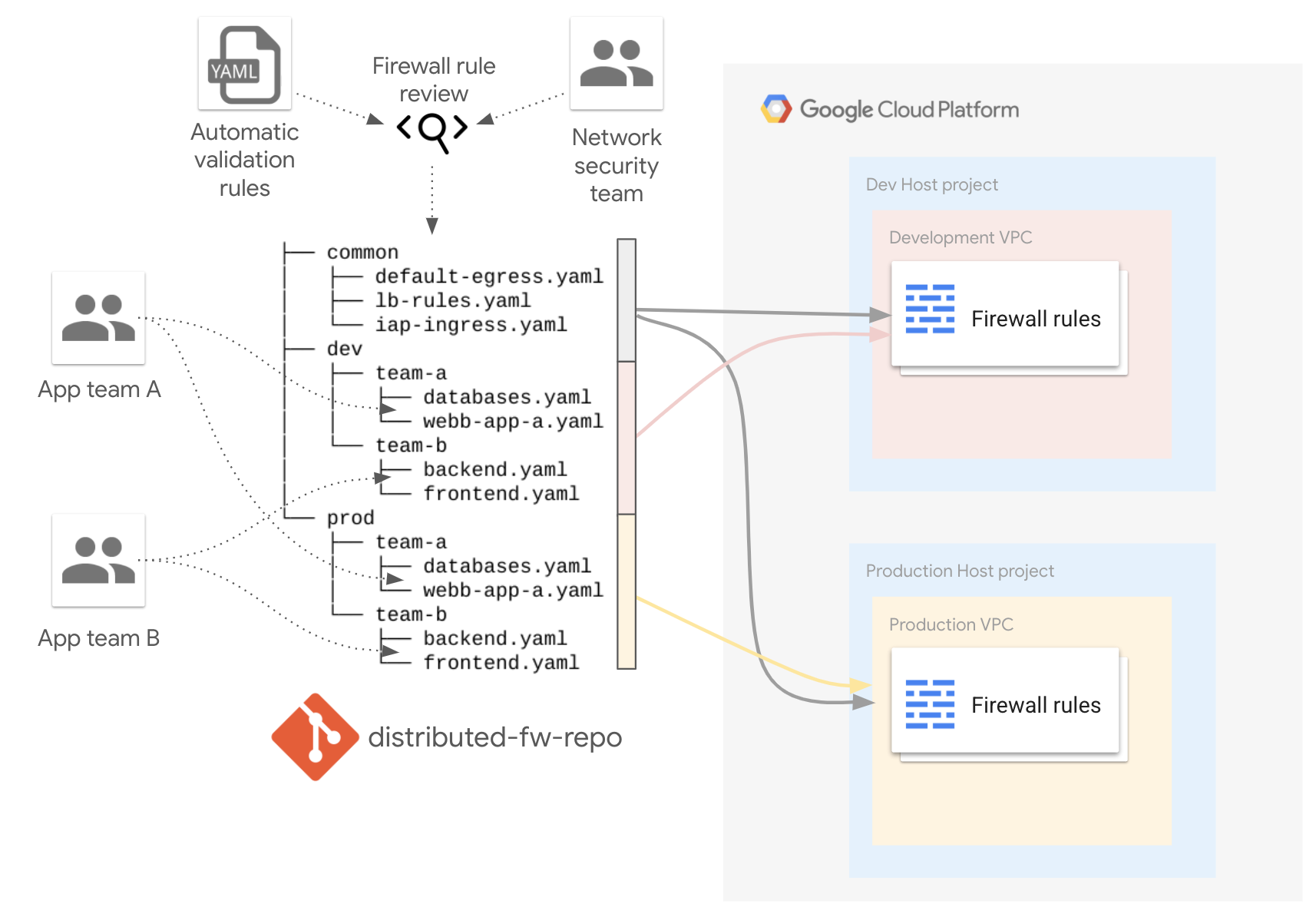 This blueprint shows how a decentralized firewall management can be organized using the firewall factory.
This blueprint shows how a decentralized firewall management can be organized using the firewall factory.
GLB and multi-regional daisy-chaining through hybrid NEGs
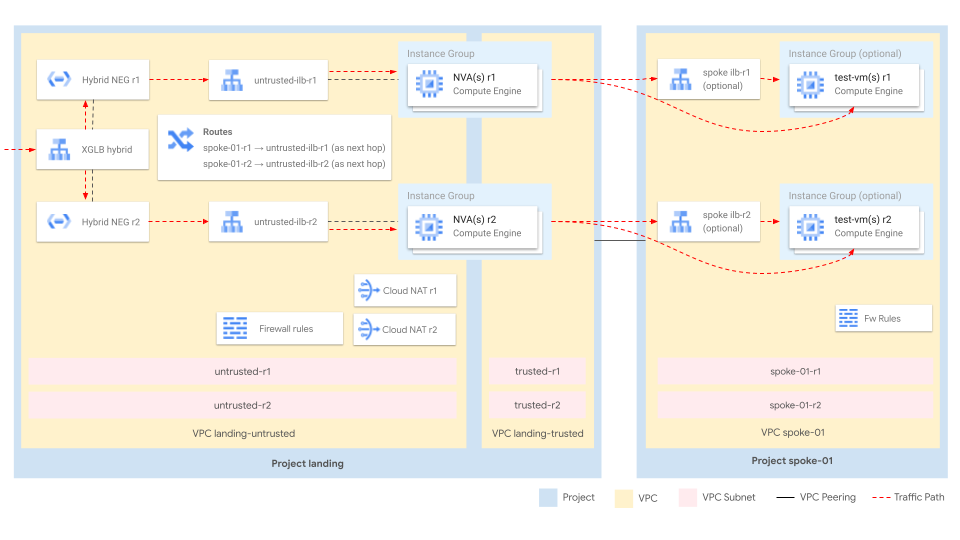 This blueprint shows the experimental use of hybrid NEGs behind external Global Load Balancers (GLBs) to connect to GCP instances living in spoke VPCs and behind Network Virtual Appliances (NVAs).
This blueprint shows the experimental use of hybrid NEGs behind external Global Load Balancers (GLBs) to connect to GCP instances living in spoke VPCs and behind Network Virtual Appliances (NVAs).
HTTP Load Balancer with Cloud Armor
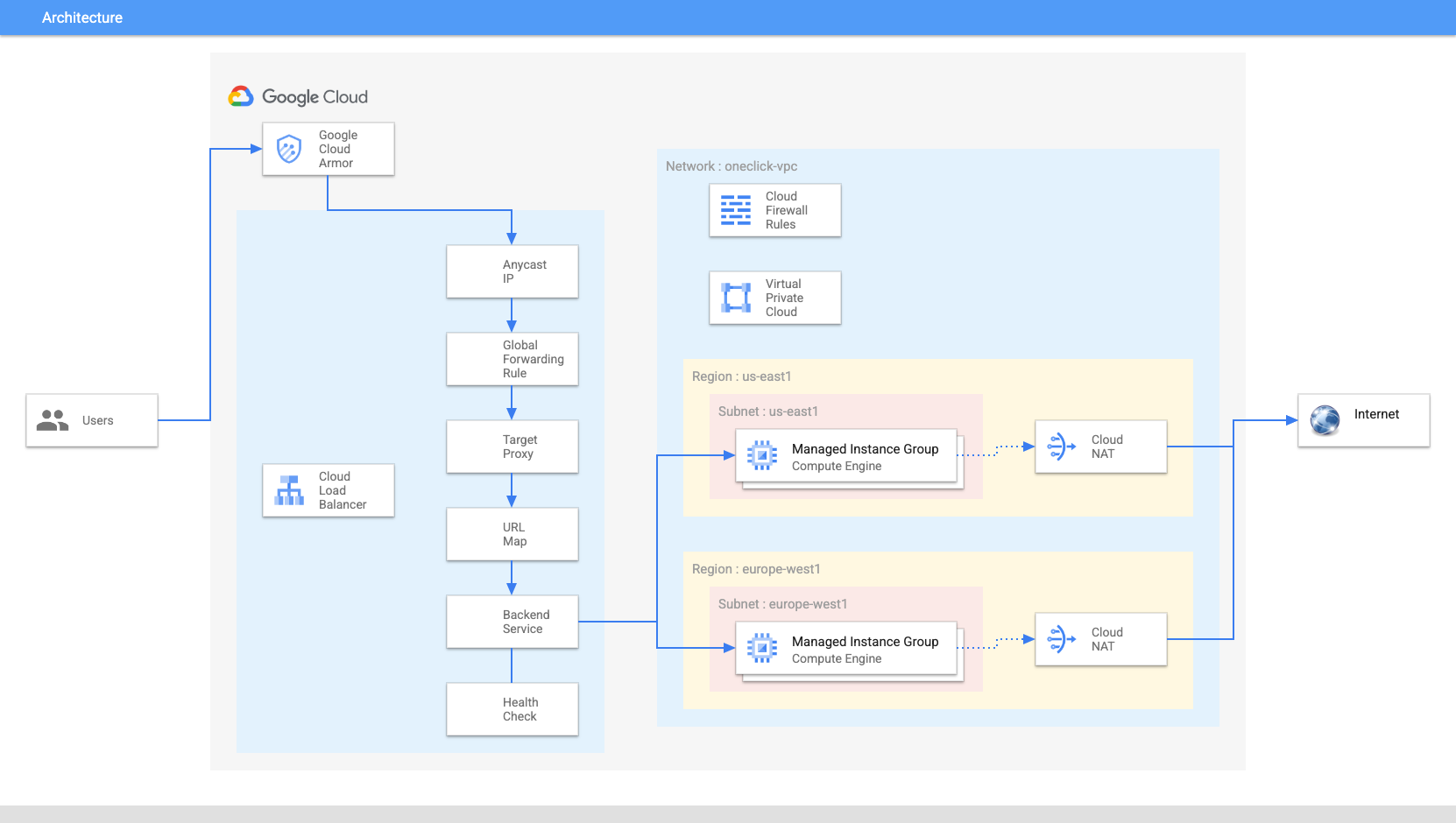 This blueprint contains all necessary Terraform modules to build a multi-regional infrastructure with horizontally scalable managed instance group backends, HTTP load balancing and Google’s advanced WAF security tool (Cloud Armor) on top to securely deploy an application at global scale.
This blueprint contains all necessary Terraform modules to build a multi-regional infrastructure with horizontally scalable managed instance group backends, HTTP load balancing and Google’s advanced WAF security tool (Cloud Armor) on top to securely deploy an application at global scale.
Hub and Spoke via Dynamic VPN
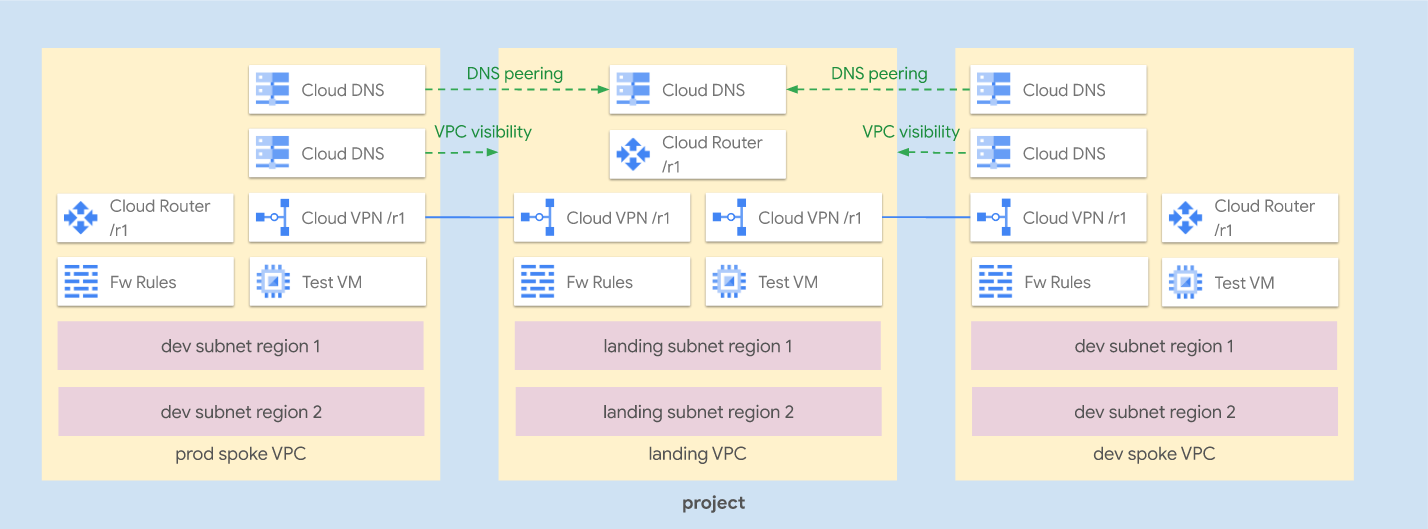 This blueprint implements a hub and spoke topology via dynamic VPN tunnels, a common design where peering cannot be used due to limitations on the number of spokes or connectivity to managed services.
This blueprint implements a hub and spoke topology via dynamic VPN tunnels, a common design where peering cannot be used due to limitations on the number of spokes or connectivity to managed services.
The blueprint shows how to implement spoke transitivity via BGP advertisements, how to expose hub DNS zones to spokes via DNS peering, and allows easy testing of different VPN and BGP configurations.
Hub and Spoke via Peering
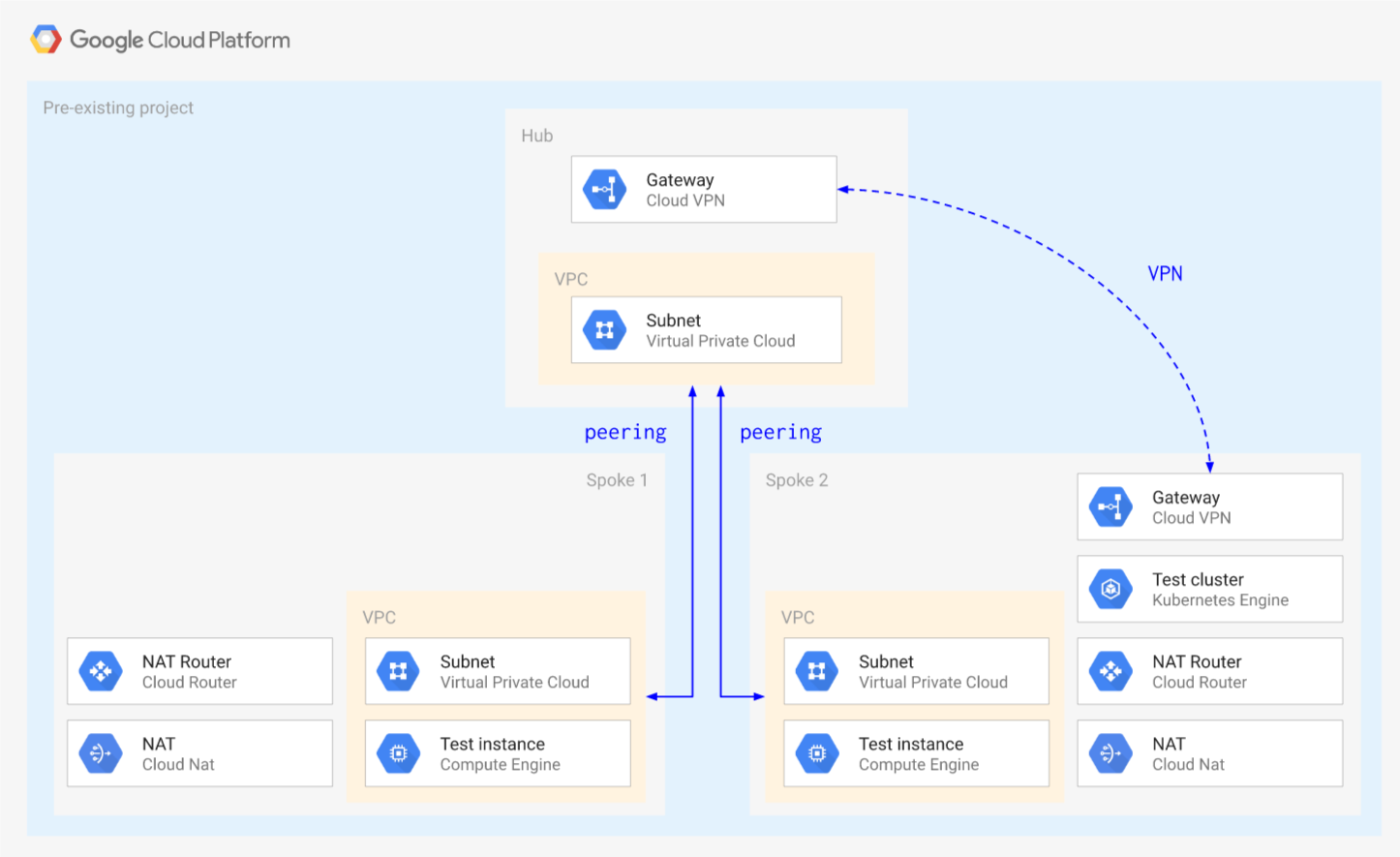 This blueprint implements a hub and spoke topology via VPC peering, a common design where a landing zone VPC (hub) is connected to on-premises, and then peered with satellite VPCs (spokes) to further partition the infrastructure.
This blueprint implements a hub and spoke topology via VPC peering, a common design where a landing zone VPC (hub) is connected to on-premises, and then peered with satellite VPCs (spokes) to further partition the infrastructure.
The sample highlights the lack of transitivity in peering: the absence of connectivity between spokes, and the need create workarounds for private service access to managed services. One such workaround is shown for private GKE, allowing access from hub and all spokes to GKE masters via a dedicated VPN.
Internal Network LB as next hop
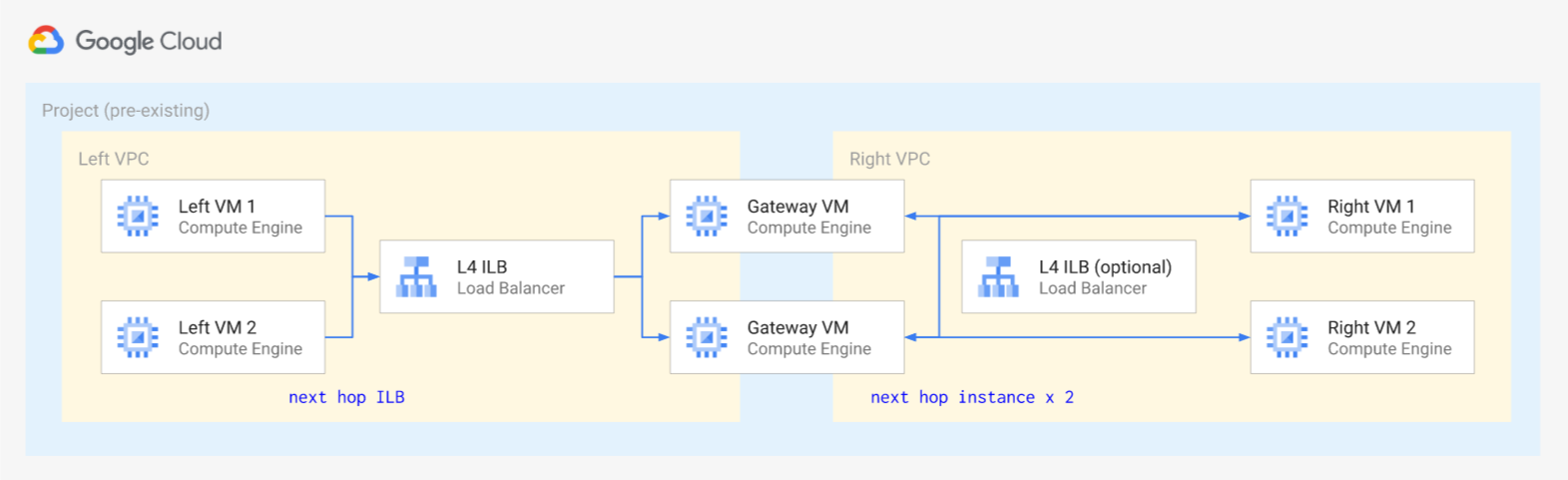 This blueprint allows testing Internal Network LB as next hop using simple Linux gateway VMS between two VPCs, to emulate virtual appliances. An optional additional Internal Network LB can be enabled to test multiple load balancer configurations and hashing.
This blueprint allows testing Internal Network LB as next hop using simple Linux gateway VMS between two VPCs, to emulate virtual appliances. An optional additional Internal Network LB can be enabled to test multiple load balancer configurations and hashing.
Network filtering with Squid
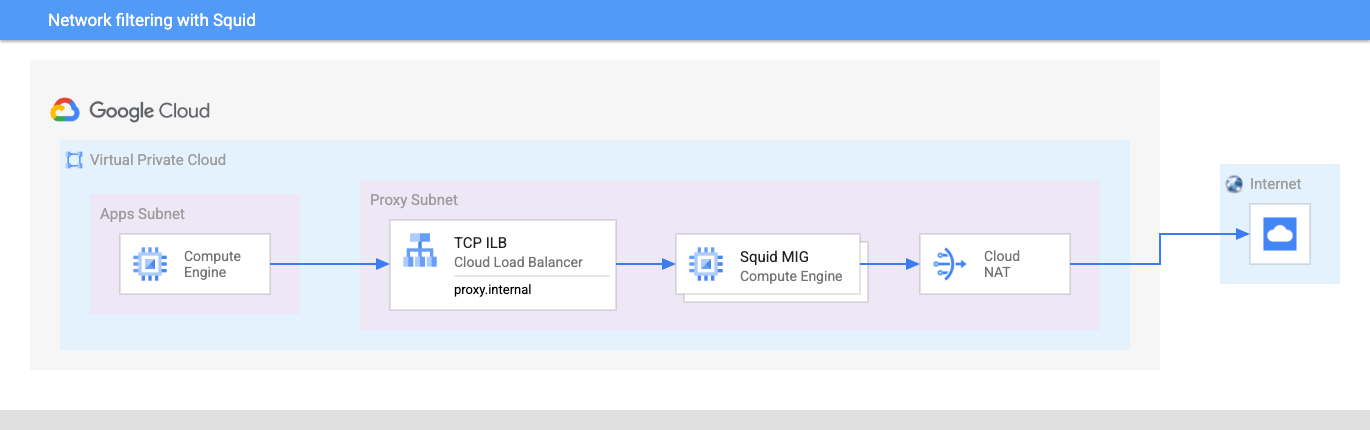 This blueprint how to deploy a filtering HTTP proxy to restrict Internet access, in a simplified setup using a VPC with two subnets and a Cloud DNS zone, and an optional MIG for scaling.
This blueprint how to deploy a filtering HTTP proxy to restrict Internet access, in a simplified setup using a VPC with two subnets and a Cloud DNS zone, and an optional MIG for scaling.
Shared VPC with GKE and per-subnet support
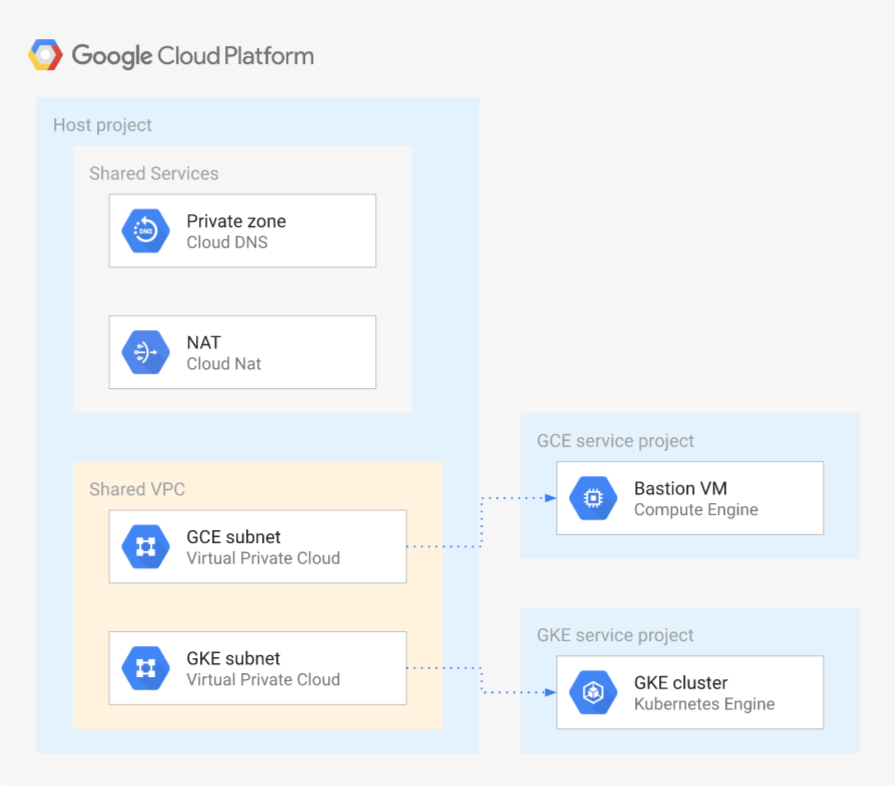 This blueprint shows how to configure a Shared VPC, including the specific IAM configurations needed for GKE, and to give different level of access to the VPC subnets to different identities.
This blueprint shows how to configure a Shared VPC, including the specific IAM configurations needed for GKE, and to give different level of access to the VPC subnets to different identities.
It is meant to be used as a starting point for most Shared VPC configurations, and to be integrated to the above blueprints where Shared VPC is needed in more complex network topologies.
Exposing applications to the internet via GCLB and Private Service Connect
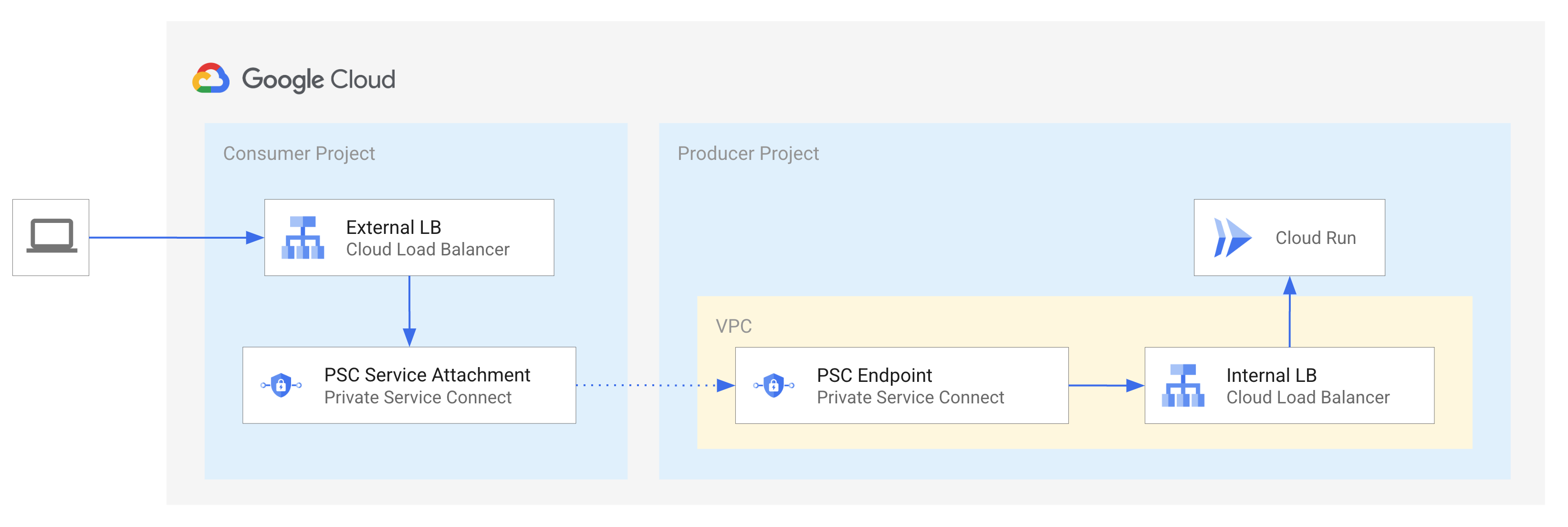 This blueprint shows how to configure an external Google Cloud Load Balancer, with a simple Cloud Armor rule to protect against DDOS attacks, to provide an external endpoint to an application provided by another team via Private Service Connect (PSC).
This blueprint shows how to configure an external Google Cloud Load Balancer, with a simple Cloud Armor rule to protect against DDOS attacks, to provide an external endpoint to an application provided by another team via Private Service Connect (PSC).
It is meant to be used as a starting point for users that want to explore PSC to reduce some of the complexity in their network setup.