* GCVE stage prerequisites * fix gcve prereq * gcve stage first deploy * Updated readme filex * docs updated * some fixes after testing * updated readme files * elia fix * gcve net admin custom role * gcve net admin custom role * elia fix * ven peering deploy * elia fix * added blueprint and stage tests * Edits to Readme files * typo in outputs * clean-up * gcve stage tests fix * readme fix * fix sorting * fix copyrights and readme file * fix test * fix copyright * fixed gcve feature flag cond. * removed validation * fixed typo * fixed typo * fixed gcve tests * fixed typo * fixed typo * fixed sorting * fixed sorting --------- Co-authored-by: Konrad Schieban <kschieban@google.com> |
||
|---|---|---|
| .. | ||
| README.md | ||
| diagram.png | ||
| gcve-pc.tf | ||
| main.tf | ||
| output.tf | ||
| variables.tf | ||
README.md
GCVE Private Cloud Minimal
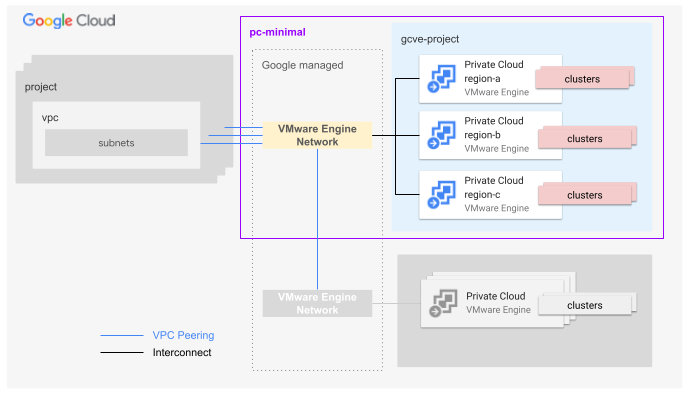
This blueprint presents an opinionated architecture to handle different Google VMware Engine deployment scenarios: from a simple single region private cloud to multi-region private clouds spread across different locations. The general idea behind this blueprint is to deploy a single project hosting one or more GCVE private clouds connected to a shared VMware Engine Network (VEN). Optionally this blueprint can deploy the VMWare Engine Network peerings to pre-existing VPCs.
Multiple deployments of this blueprint allow the user to achieve more complex design solutions as for example GCVE private clouds deployed on different projects or connected to indipendent VMWare Engine Networks.
This blueprint is used as part of the FAST GCVE stage but it can also be used independently if desired.
The blueprint manages:
- project creation
- project-level organization policy definitions
- billing setup (billing account attachment)
- API/services enablement
- IAM role assignment for groups
- VMware Engine private clouds creation
- VMware Engine Network creation
- VPC attachment (Optional)
User groups
Based on our GCP best practices, a GCVE private cloud relies on user groups to assign roles to human identities. These are the specific groups bound to the main GCVE predefined roles:
- VMware Engine Administrators. They have full access to the VMWare Engine Service.
- VMware Engine Viewers. They have read-only access to the VMware Engine Service.
Network
This blueprints expects the user to provision a VPC upfront, either from one of the FAST networking stages (e.g. Networking with separated single environment) or from an external source. The blueprint can optionally configure the VMware Engine Network peering on the peer VPC by granting the following permissions on the project that hosts the VPC:
- vmwareengine.networkPeerings.create
- vmwareengine.networkPeerings.get
- vmwareengine.networkPeerings.list
- vmwareengine.operations.get The permissions can be assigned through the predefined role vmwareengine.vmwareengineAdmin. Anyway the creation of a dedicated custom roile is strogly recommended to comply with the least privilege principle.
Basic usage
The following example shows how to deploy a CGVE private cloud and connect it to a VPC
module "gcve-pc" {
source = "./fabric/blueprints/gcve/pc-minimal"
billing_account_id = "000000-000000-000000"
folder_id = "folders/000000000000"
project_id = "myprojectid"
groups = {
gcp-gcve-admins = "group:gcp-gcve-admins@acme.com"
gcp-gcve-viewers = "group:gcp-gcve-viewers@acme.com"
}
prefix = "myprefix"
network_peerings = {
dev-spoke-ven = {
peer_network = "projects/spokeproject/regions/europe-west1/subnetworks/dev-default-ew1"
peer_project_id = "peerprojectid"
}
}
private_cloud_configs = {
dev-pc = {
cidr = "172.26.16.0/22"
zone = "europe-west1-a"
management_cluster_config = {
name = "mgmt-cluster"
node_count = 1
node_type_id = "standard-72"
}
}
}
}
# tftest modules=3 resources=7
Files
| name | description | modules | resources |
|---|---|---|---|
| gcve-pc.tf | GCVE private cloud. | gcve-private-cloud |
google_vmwareengine_network_peering |
| main.tf | Project. | project |
|
| output.tf | Output variables. | ||
| variables.tf | Module variables. |
Variables
| name | description | type | required | default |
|---|---|---|---|---|
| billing_account_id | Billing account ID. | string |
✓ | |
| folder_id | Folder used for the GCVE project in folders/nnnnnnnnnnn format. | string |
✓ | |
| groups | GCVE groups. | object({…}) |
✓ | |
| prefix | Prefix used for resource names. | string |
✓ | |
| private_cloud_configs | The VMware private cloud configurations. The key is the unique private cloud name suffix. | map(object({…})) |
✓ | |
| project_id | ID of the project that will contain the GCVE private cloud. | string |
✓ | |
| iam | Project-level authoritative IAM bindings for users and service accounts in {ROLE => [MEMBERS]} format. | map(list(string)) |
{} |
|
| iam_by_principals | Authoritative IAM binding in {PRINCIPAL => [ROLES]} format. Principals need to be statically defined to avoid cycle errors. Merged internally with the iam variable. |
map(list(string)) |
{} |
|
| labels | Project-level labels. | map(string) |
{} |
|
| network_peerings | The network peerings between users' VPCs and the VMware Engine networks. The key is the peering name suffix. | map(object({…})) |
{} |
|
| project_services | Additional project services to enable. | list(string) |
[] |