|
|
||
|---|---|---|
| .github | ||
| accounts | ||
| bmt | ||
| build | ||
| cmd | ||
| common | ||
| consensus | ||
| console | ||
| containers | ||
| contracts | ||
| core | ||
| crypto | ||
| dashboard | ||
| docs | ||
| eth | ||
| ethclient | ||
| ethdb | ||
| ethstats | ||
| event | ||
| internal | ||
| les | ||
| light | ||
| log | ||
| metrics | ||
| miner | ||
| mobile | ||
| node | ||
| p2p | ||
| params | ||
| permission | ||
| private | ||
| raft | ||
| rlp | ||
| rpc | ||
| signer | ||
| swarm | ||
| tests | ||
| trie | ||
| vendor | ||
| whisper | ||
| .bintray.json | ||
| .dockerignore | ||
| .gitattributes | ||
| .gitignore | ||
| .gitmodules | ||
| .mailmap | ||
| .travis.yml | ||
| AUTHORS | ||
| BUILDING.md | ||
| COPYING | ||
| COPYING.LESSER | ||
| Dockerfile | ||
| Dockerfile.alltools | ||
| Makefile | ||
| NOTES.md | ||
| README.md | ||
| appveyor.yml | ||
| circle.yml | ||
| interfaces.go | ||
| logo.png | ||
| mkdocs.yml | ||
README.md
Quorum is an Ethereum-based distributed ledger protocol with transaction/contract privacy and new consensus mechanisms.
Quorum is a fork of go-ethereum and is updated in line with go-ethereum releases.
Key enhancements over go-ethereum:
- Privacy - Quorum supports private transactions and private contracts through public/private state separation, and utilises peer-to-peer encrypted message exchanges (see Constellation and Tessera) for directed transfer of private data to network participants
- Alternative Consensus Mechanisms - with no need for POW/POS in a permissioned network, Quorum instead offers multiple consensus mechanisms that are more appropriate for consortium chains:
- Raft-based Consensus - a consensus model for faster blocktimes, transaction finality, and on-demand block creation
- Istanbul BFT - a PBFT-inspired consensus algorithm with transaction finality, by AMIS.
- Peer Permissioning - node/peer permissioning using smart contracts, ensuring only known parties can join the network
- Higher Performance - Quorum offers significantly higher performance than public geth
Architecture
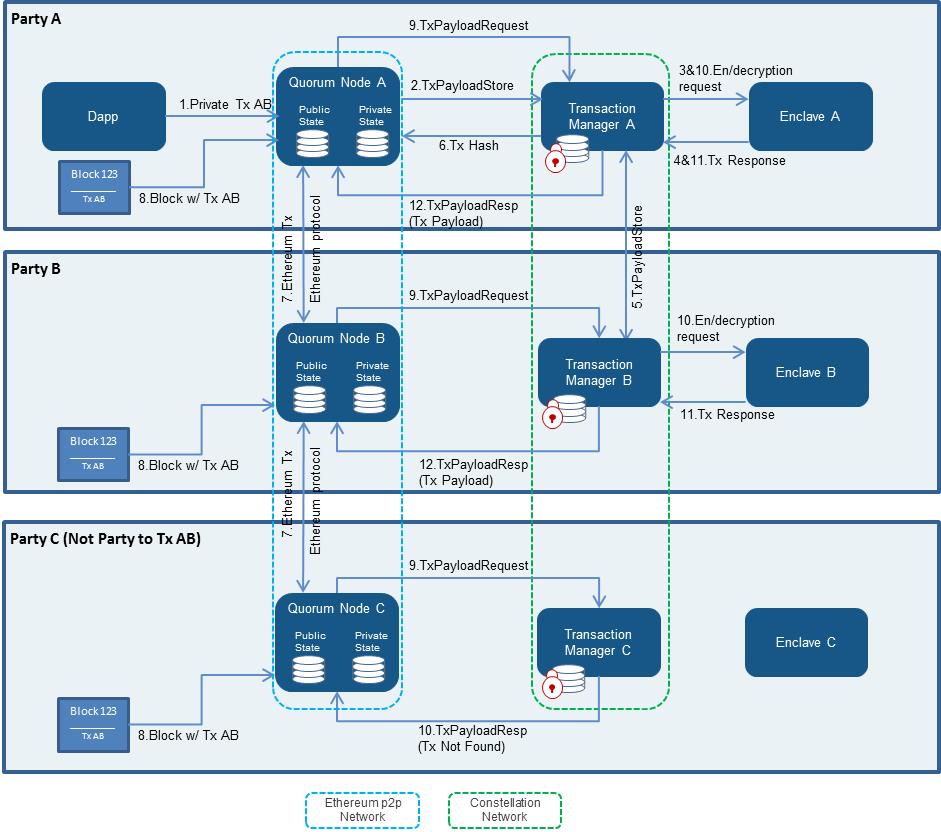
The above diagram is a high-level overview of the privacy architecture used by Quorum. For more in-depth discussion of the components, refer to the documentation site.
Quickstart
The quickest way to get started with Quorum is by following instructions in the Quorum Examples repository. This allows you to quickly create a network of Quorum nodes, and includes a step-by-step demonstration of the privacy features of Quorum.
Further Reading
Further documentation can be found in the docs folder and on the documentation site.
Official Docker Containers
The official docker containers can be found under https://hub.docker.com/u/quorumengineering/
See also
- Quorum: this repository
- Quorum Documentation
- quorum-examples: Quorum demonstration examples
- Quorum Community Slack Inviter: Quorum Slack community entry point
- Quorum Transaction Managers
- Constellation: Haskell implementation of peer-to-peer encrypted message exchange for transaction privacy
- Tessera: Java implementation of peer-to-peer encrypted message exchange for transaction privacy
- Quorum supported consensuses
- Raft Consensus Documentation
- Istanbul BFT Consensus Documentation: RPC API and technical article. Please note that updated istanbul-tools is now hosted in this repository
- Clique POA Consensus Documentation and a guide to setup clique json with puppeth
- Zero Knowledge on Quorum
- ZSL wiki page and documentation
- Anonymous Zether implementation
- quorum-cloud: Tools to help deploy Quorum network in a cloud provider of choice
- Cakeshop: An integrated development environment and SDK for Quorum
Third Party Tools/Libraries
The following Quorum-related libraries/applications have been created by Third Parties and as such are not specifically endorsed by J.P. Morgan. A big thanks to the developers for improving the tooling around Quorum!
- Quorum Blockchain Explorer - a Blockchain Explorer for Quorum which supports viewing private transactions
- Quorum-Genesis - A simple CL utility for Quorum to help populate the genesis file with voters and makers
- Quorum Maker - a utility to create Quorum nodes
- QuorumNetworkManager - makes creating & managing Quorum networks easy
- ERC20 REST service - a Quorum-supported RESTful service for creating and managing ERC-20 tokens
- Nethereum Quorum - a .NET Quorum adapter
- web3j-quorum - an extension to the web3j Java library providing support for the Quorum API
- Apache Camel - an Apache Camel component providing support for the Quorum API using web3j library. Here is the artcile describing how to use Apache Camel with Ethereum and Quorum https://medium.com/@bibryam/enterprise-integration-for-ethereum-fa67a1577d43
Contributing
Quorum is built on open source and we invite you to contribute enhancements. Upon review you will be required to complete a Contributor License Agreement (CLA) before we are able to merge. If you have any questions about the contribution process, please feel free to send an email to info@goquorum.com.
Reporting Security Bugs
Security is part of our commitment to our users. At Quorum we have a close relationship with the security community, we understand the realm, and encourage security researchers to become part of our mission of building secure reliable software. This section explains how to submit security bugs, and what to expect in return.
All security bugs in Quorum and its ecosystem (Tessera, Constellation, Cakeshop, ..etc) should be reported by email to info@goquorum.com. Please use the prefix [security] in your subject. This email is delivered to Quorum security team. Your email will be acknowledged, and you'll receive a more detailed response to your email as soon as possible indicating the next steps in handling your report. After the initial reply to your report, the security team will endeavor to keep you informed of the progress being made towards a fix and full announcement.
If you have not received a reply to your email or you have not heard from the security team please contact any team member through quorum slack security channel. Please note that Quorum slack channels are public discussion forum. When escalating to this medium, please do not disclose the details of the issue. Simply state that you're trying to reach a member of the security team.
Responsible Disclosure Process
Quorum project uses the following responsible disclosure process:
- Once the security report is received it is assigned a primary handler. This person coordinates the fix and release process.
- The issue is confirmed and a list of affected software is determined.
- Code is audited to find any potential similar problems.
- If it is determined, in consultation with the submitter, that a CVE-ID is required, the primary handler will trigger the process.
- Fixes are applied to the public repository and a new release is issued.
- On the date that the fixes are applied, announcements are sent to Quorum-announce.
- At this point you would be able to disclose publicly your finding.
Note: This process can take some time. Every effort will be made to handle the security bug in as timely a manner as possible, however it's important that we follow the process described above to ensure that disclosures are handled consistently.
Receiving Security Updates
The best way to receive security announcements is to subscribe to the Quorum-announce mailing list/channel. Any messages pertaining to a security issue will be prefixed with [security].
Comments on This Policy If you have any suggestions to improve this policy, please send an email to info@goquorum.com for discussion.
License
The go-ethereum library (i.e. all code outside of the cmd directory) is licensed under the
GNU Lesser General Public License v3.0, also
included in our repository in the COPYING.LESSER file.
The go-ethereum binaries (i.e. all code inside of the cmd directory) is licensed under the
GNU General Public License v3.0, also included
in our repository in the COPYING file.